
A new ransomware called B0r0nt0K is encrypting victim's web sites and demanding a 20 bitcoin, or approximately $75,000, ransom. This ransomware is known to infect Linux servers, but may also be able to encrypt users running Windows.
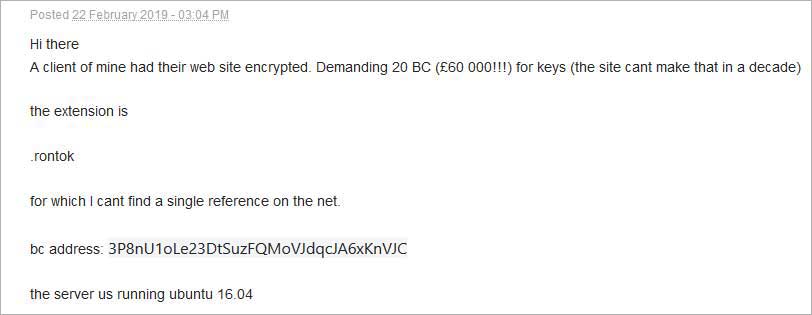
In a BleepingComputer forum post, a user stated that a client's web site was encrypted with the new B0r0nt0K Ransomware. This encrypted web site was running on Ubuntu 16.04 and had all of its files encrypted, renamed, and had the .rontok extension appended to them.
As a sample of the ransomware has not been found, there is not much information other than what we have learned from the submitted files and by examining the payment site.
According to Michael Gillespie, when B0r0nt0K encrypts a file it will base64 the encrypted data as shown below.
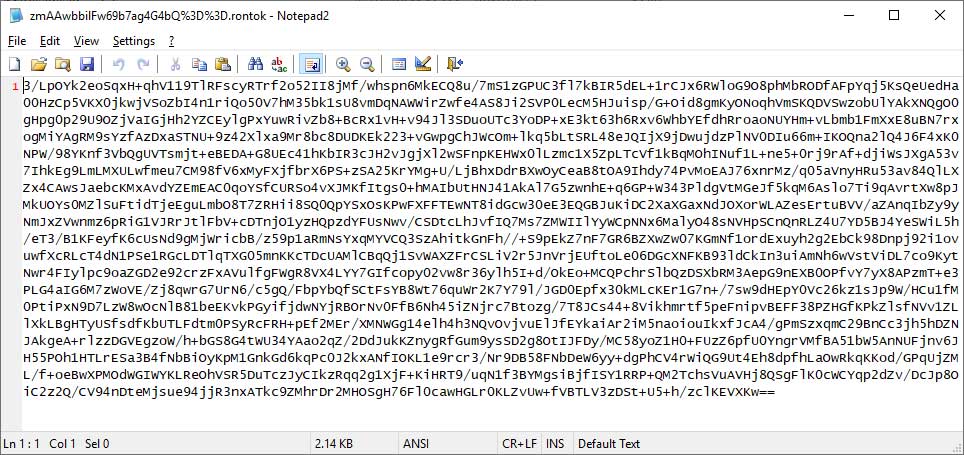
The file's name will also be renamed by encrypting the filename, base64 encoding it, url encoding it, and finally appending the .rontok extension to the new file name. An example of a encrypted file's name is zmAAwbbilFw69b7ag4G4bQ%3D%3D.rontok.
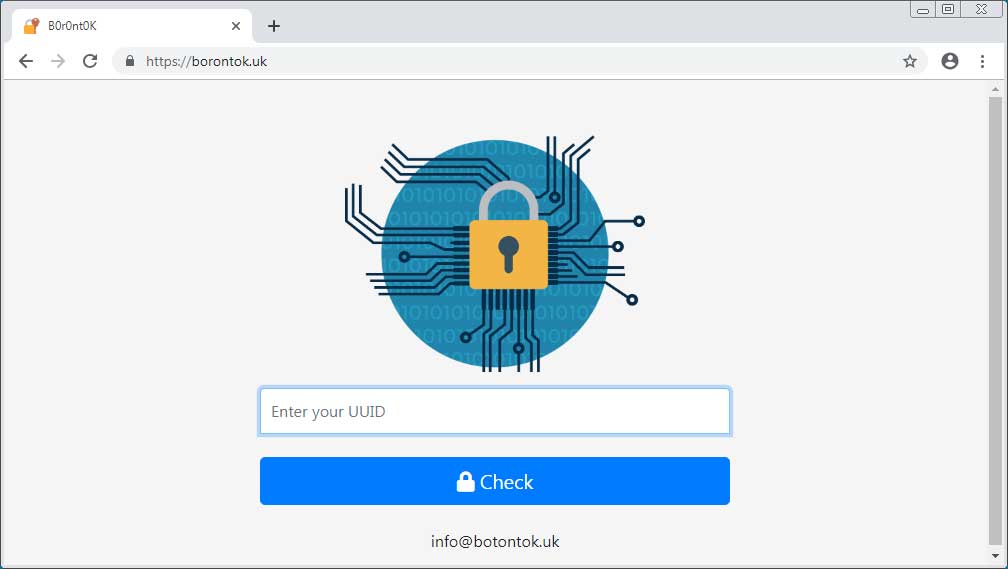
While the user was not able to provide a ransom note, he was able to provide the URL of the payment site located at https://borontok.uk/. When visiting this site, the user will be asked to submit their personal ID.
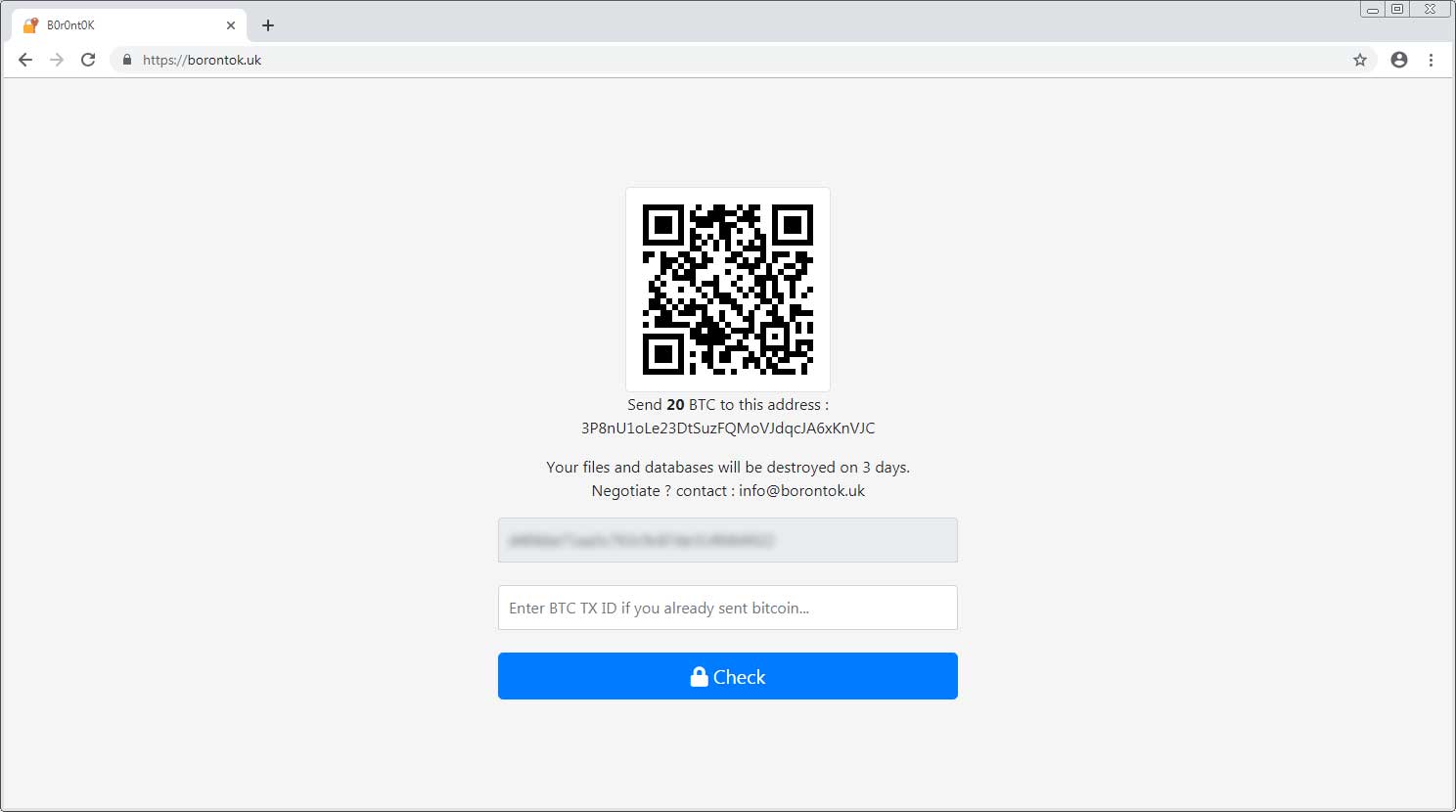
Once an ID is entered, the user will be presented with a payment page that includes a the bitcoin ransom amount, the bitcoin payment address, and the info@botontok.uk email that can be used to contact the developers. In this particular instance, the ransom demand was 20 bitcoins, which is currently equal to approximately $75,000. The developers, though, appear to be willing to negotiate the price.
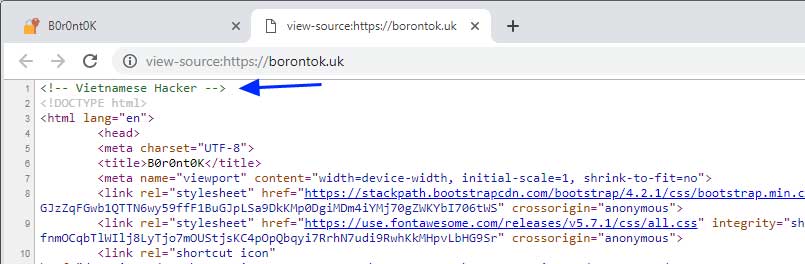
When examining the source code for the payment site, BleepingComputer noticed the "Vietnamese Hacker" embedded comment. While this could indicate that the developer is Vietnamese, this is by no means proof.
BleepingComputer has contacted the author of this ransomware for more information, but has not heard back as of yet. We will update this article as new information becomes available.


Comments
GT500 - 5 years ago
I wonder what the infection vector was. Brute forced SSH/VNC/FTP? An HTTP server vulnerability?
I'm fairly paranoid, and keep the SSH and FTP ports closed. I add port rules on a per-IP basis so that those who need access can have it, and so that no one else can probe my SSH/FTP ports. I also set up a daily update script for sensitive services like the HTTP server, PHP, IMAP, SMTP, etc.
Lawrence Abrams - 5 years ago
As it's a website, my guess its a CMS vuln.
GT500 - 5 years ago
More than likely. That stuff is rather dangerous these days.
tvshub - 5 years ago
So what if every time someone gets hit with ransomware, the crooks contact email is publish to an email list of 1000's of people who all send them an email? Call it denial of ransom - DoR. How is this scam still going on? And using Bitcoin certainly isn't helping cryptocurrencies gain any respect.